You're probably here for one of two reasons. Either you need the domain name of the machine in front of you, fast, because an audit script, inventory job, or migration task is waiting. Or you typed get domain name powershell and expected a one-liner, then realized half the internet mixes local machine info, Active Directory info, and public web domain checks like they're the same thing.
They're not the same thing, but the mindset is.
The same PowerShell habits that make you good at internal domain work, querying cleanly, handling ugly edge cases, and packaging output into something useful, also make you surprisingly effective at hunting public domains for SEO, branding, and investment. A sysadmin already knows how to automate checks, trust objects over screenshots, and ignore noisy tools that don't scale. That skill set transfers better than many realize.
Why Your PowerShell Skills Are a Domain Finding Superpower
A lot of admins first learn domain lookups in the least glamorous way possible. A server fails a login policy check. A laptop lands in the wrong OU. A script needs to know whether the box is in the right domain before it does anything risky. You grab the domain name, move on, and forget about it.
That routine task hides a useful pattern. You're validating identity, context, and ownership before taking action. That's the exact same discipline good domain buyers use when they evaluate names on the public internet. The details change, but the workflow doesn't.
A network domain and a web domain also get conflated constantly, which is why it helps to keep the distinction crisp. If you need a quick reset on that difference, this breakdown of what a domain means in networking is worth a skim.
The admins who write the best audit scripts usually make the best domain researchers too. They already know how to ask better questions before they trust an answer.
The big shift is this. Inside your network, PowerShell tells you what domain a system belongs to and how that environment is structured. Outside your network, PowerShell can help you inspect whether a public domain resolves, whether it looks active, and whether it deserves deeper review.
That's where things get fun. The command line stops being just an IT wrench and starts acting like a scouting tool.
The Local Lowdown Grabbing Your Workstation's Domain
When someone asks how to get a domain name in PowerShell, they usually mean the local machine or the logged-on user context. There are three practical ways to do it, and each one has a different sweet spot.
Use .NET when you want the actual AD domain context
If the machine is domain-joined and you want the Fully Qualified Domain Name, this is the cleanest native option:
$strDomainDNS = [System.DirectoryServices.ActiveDirectory.Domain]::GetCurrentDomain().Name
That command uses the static GetCurrentDomain() method, performs an LDAP bind against the local directory context, and has a success rate exceeding 99% in domain-joined Windows environments (Server 2008+), according to the Netnerds walkthrough on retrieving the current AD domain FQDN.
Why I like it:
- It returns the actual AD domain name instead of a guess based on local naming.
- It doesn't require the ActiveDirectory module.
- It fits well in scripts where you want consistent directory-aware output.
When it fails, it usually fails for a good reason. The machine isn't domain-joined, the current context is wrong, or the domain can't be contacted.
Use the environment variable when you need speed and simplicity
For a quick answer in an interactive shell, this is hard to beat:
$env:USERDNSDOMAIN
This works well when the user is logged on in a domain context and you just need the current user's DNS domain. It's lightweight and easy to read.
The downside is simple. It reflects the logged-on user environment, not a deeper directory lookup. If I'm writing something that may run under different security contexts, scheduled tasks, or odd session states, I don't treat this as the final word.
Practical rule: If a failed answer would break automation, use the .NET method. If you're sanity-checking your own session,
$env:USERDNSDOMAINis usually enough.
Use WMI when you need broad compatibility or machine-level context
The old-school option still earns its keep:
(Get-WmiObject Win32_ComputerSystem).Domain
This is useful when you care about the computer's domain membership rather than the current user's session. It's also handy in mixed environments where you're already pulling other Win32_ComputerSystem properties and want one pass through the same object.
A quick comparison helps:
| Method | Best for | Trade-off |
|---|---|---|
[System.DirectoryServices.ActiveDirectory.Domain]::GetCurrentDomain().Name |
Accurate AD FQDN lookup | Requires domain context to succeed |
$env:USERDNSDOMAIN |
Fast interactive checks | Tied to user logon context |
(Get-WmiObject Win32_ComputerSystem).Domain |
Machine membership checks | Older style and less directory-specific |
If you only remember one thing, remember this: pick the command based on what you're trying to prove. User context, machine membership, and live directory context are related, but they aren't identical.
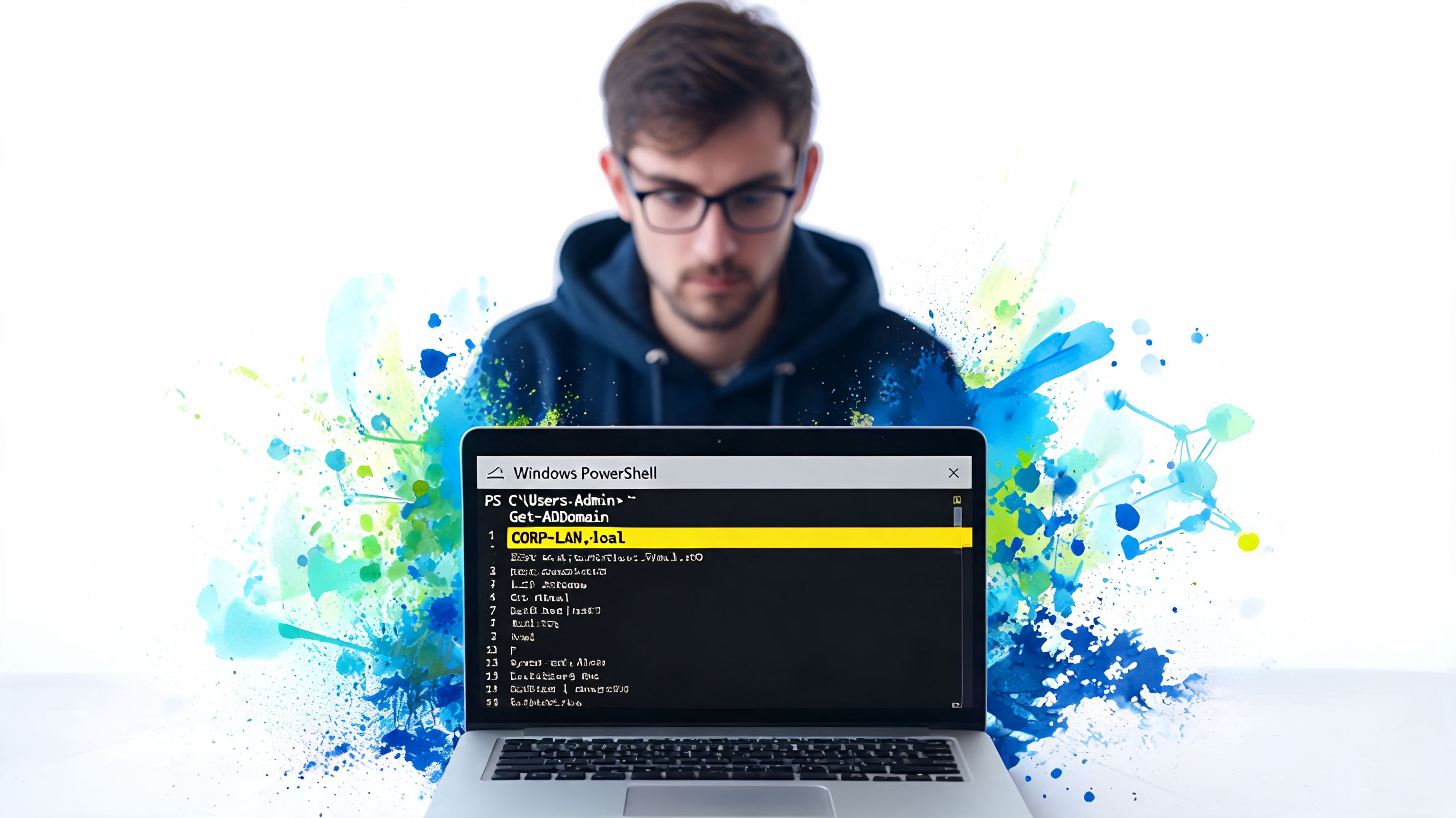
Mastering Active Directory with Get-ADDomain
Once you leave the local box and step into enterprise AD, Get-ADDomain becomes the command that saves time, reduces guesswork, and tells you whether the environment is as tidy as people claim it is.
Microsoft introduced Get-ADDomain with Windows Server 2008 R2, and it changed AD administration by giving admins a structured, queryable way to retrieve domain metadata. A 2023 Spiceworks survey found that 78% of IT pros use PowerShell for AD tasks, with Get-ADDomain cited in 42% of domain management scripts, as summarized in the Microsoft cmdlet documentation.
Start with the domain object, not scattered commands
The basic call is straightforward:
Get-ADDomain
If you're on a domain-joined machine with the ActiveDirectory module available, that one line returns a rich object. Not a blob of text. An object you can filter, select, export, and compare.
That matters because domain work usually turns into follow-up work. You don't just want the name. You want to know which controllers are tied to it, what the functional level is, and where the critical roles live.
A few examples:
Get-ADDomain | Select-Object DNSRoot, NetBIOSName
Get-ADDomain | Select-Object DomainMode, Forest, ParentDomain
Get-ADDomain | Select-Object PDCEmulator, InfrastructureMaster, RIDMaster
Pull what matters during audits and migrations
If I'm checking an environment before change work, these are the properties I care about first:
DNSRootfor the actual DNS name of the domainDomainModeto confirm the domain functional levelReplicaDirectoryServersor domain controller-related properties to understand controller placement- FSMO holders like
PDCEmulatorandRIDMasterso there are no surprises when something starts behaving oddly
If you're managing an upgrade or a cleanup project, an essential AD guide for IT managers can help frame the bigger design questions around directory structure and deployment choices.
Here's a good habit. Don't dump the whole object to the screen and scroll until your eyes glaze over. Target the properties that answer the operational question in front of you.
A messy AD environment usually reveals itself in the first few selected properties. You don't need ten pages of output to spot drift.
Later, if you want a visual walkthrough before putting the cmdlet into production scripts, this video gives a practical admin-focused view:
Use identity targeting when default context isn't enough
Get-ADDomain gets even better when you stop assuming your current machine context is the right one.
Get-ADDomain -Identity contoso.com
The cmdlet accepts multiple identity formats, including DNS name, GUID, SID, distinguished name, and NetBIOS name. That makes it useful in larger estates where naming isn't always tidy and where scripts may need to target a specific domain directly.
Short version: if you work in AD and you're still using brittle workarounds for basic domain metadata, you're making life harder than it needs to be.
Going Remote Querying Domains Across Your Network
One machine is a check. A fleet is an inventory.
Remote domain querying is where PowerShell starts paying rent. Instead of RDPing into boxes, clicking through system properties, or trying to remember which server belongs where, you can ask every target the same question and collect the answer in a format that's useful.

There's a reason admins keep building remote info-gathering scripts. The Get-ADInfo.ps1 script, which leans heavily on cmdlets like Get-ADDomain inside remote execution blocks, has been downloaded over 150,000 times since 2020, and remote checks can be up to 95% faster than manual checks with RSAT, according to the PowerShell forum discussion that references that workflow.
A practical remote pattern
This is a solid starting point for querying domain information from multiple machines:
$computers = Get-Content .\computers.txt
$results = foreach ($computer in $computers) {
try {
Invoke-Command -ComputerName $computer -ScriptBlock {
[pscustomobject]@{
ComputerName = $env:COMPUTERNAME
UserDNSDomain = $env:USERDNSDOMAIN
MachineDomain = (Get-WmiObject Win32_ComputerSystem).Domain
}
} -ErrorAction Stop
}
catch {
[pscustomobject]@{
ComputerName = $computer
UserDNSDomain = $null
MachineDomain = $null
Error = $_.Exception.Message
}
}
}
$results
That structure matters more than the exact fields. You want a script that returns a usable object even when something fails.
What breaks in the real world
Remote jobs fail for boring reasons:
- The machine is offline
- PowerShell remoting isn't enabled or reachable
- The account can connect, but not execute what you need
- The endpoint returns partial data because the user context is weird
That's why try...catch isn't optional. If your script dies on the first bad endpoint, it's not an operations script. It's a lab demo.
A good remote script should always return these three things:
- The target you attempted
- The result you got
- The reason it failed, if it failed
If you can't sort success from failure in one exported CSV, the script still needs work.
Security and exposure still matter
Remote collection also gives you a chance to spot machines that expose more than they should. Internal inventory and external attack surface reviews are different jobs, but they touch the same reality. If you want a sharper view of what public-facing assets can reveal from the outside, this guide on affordable external pentesting is a useful companion read.
The best remote scripts are boring in the best way. They run the same every time, handle ugly edge cases, and give you output you can trust without hand-editing it afterward.
From Sysadmin to Domain Hunter with PowerShell
Here's where the get domain name powershell topic gets more interesting than most tutorials allow.
Internal domain checks tell you about ownership and environment. Public domain checks tell you about presence and status. Those are different questions, but the workflow is still familiar: take a list, query it, normalize the output, flag the weird stuff, then decide what deserves deeper review.
The catch is important. Current PowerShell guides focus on technical DNS and Active Directory lookups but offer zero guidance on validating domain quality metrics like Trust Flow or backlink history, which leaves SEO professionals and domain flippers doing those checks manually, as noted in this analysis of the gap between PowerShell checks and domain quality validation.
PowerShell can verify technical signals, not investment quality
For public domain hunting, Resolve-DnsName is the native cmdlet I reach for before I ever open a browser. It's good at answering technical questions such as:
- Does the domain resolve?
- Are there records that suggest the name is active?
- Does the response look empty, broken, or in transition?
A simple pattern looks like this:
$domains = @(
"example-one.com",
"example-two.com",
"example-three.com"
)
foreach ($domain in $domains) {
try {
$result = Resolve-DnsName -Name $domain -ErrorAction Stop
[pscustomobject]@{
Domain = $domain
Status = "Resolves"
Notes = "Has public DNS response"
}
}
catch {
[pscustomobject]@{
Domain = $domain
Status = "No resolution or lookup failed"
Notes = $_.Exception.Message
}
}
}
That won't tell you whether a name is worth buying. It tells you whether the name is doing something on the public internet right now.
A better hunting workflow
The useful move is to split domain hunting into two passes.
| Pass | What PowerShell does well | What it does not answer |
|---|---|---|
| Technical pass | Checks DNS behavior, basic resolution status, repeatable bulk processing | Brandability, link quality, spam history |
| Quality pass | Organizes exportable input for downstream review | True SEO value without outside metrics |
That distinction saves time. If a domain looks technically dead, inconsistent, or strangely configured, you can flag it before spending effort on deeper research.
If you're pulling names from lists of recently dropped or soon-to-drop domains, a simple loop becomes handy. You can feed in candidates, test technical behavior in bulk, and separate names that deserve a closer look from names that are obviously noisy.
Public DNS checks are a filter, not a verdict. They help you narrow the pile.
Why this matters to admins more than they think
Admins already know how to deal with stale records, inconsistent naming, and systems that look healthy until you inspect them. Public domains behave the same way. A nice-looking name can have ugly history. A dead-looking name can be a clean opportunity. Technical checks help you sort, not decide.
That's also why cleanup matters when you move in the opposite direction. If you've ever worked through domain detachment and machine reassignment, you know context changes leave residue. This guide on removing a machine from a domain is a good reminder that domain relationships always have after-effects, whether you're managing Windows endpoints or investigating web properties.
The true benefit is mental. Once you stop treating PowerShell as only an internal admin shell, you start using it as a repeatable research engine. That's useful whether you're validating corporate assets or screening names for a side project, a redirect strategy, or a brandable acquisition.
Putting It All Together Your PowerShell Domain Toolkit
The commands matter. The toolkit mindset matters more.
For quick local checks, use the lightweight option that matches the question. For domain-joined certainty, use the .NET lookup. For machine membership, use the system object. In AD, let Get-ADDomain do the heavy lifting instead of piecing together scraps from older tools. Across the network, use remoting with proper error handling so your output survives contact with reality. For public names, use Resolve-DnsName to perform technical triage before you spend time on deeper evaluation.
That's the practical shape of get domain name powershell when you stop treating it like a one-line search query and start treating it like an operations skill. You're building a chain of trust from endpoint to directory to remote fleet to public internet.
One more habit makes the whole toolkit better. Learn the DNS records behind the answers you're seeing. If you want a clean refresher, this guide to what DNS entries are and why they matter helps connect lookup output to real-world meaning.
The admins who get the most value from PowerShell don't just retrieve information. They structure it, compare it, and act on it. That same discipline works whether you're cleaning up an enterprise environment or screening domains that might become your next project.
If you want to take the public-domain side of this further, NameSnag makes the messy part easier. You can browse available domains that already dropped and can be registered now, or review expiring domains that are still in the drop pipeline. The time filters make it easy to work today's list or widen your search window, and it pairs nicely with the PowerShell workflows above when you want to shortlist faster and research smarter.
Find Your Perfect Domain
Get access to thousands of high-value expired domains with our AI-powered search.
Start Free Trial


